Network Insight Report for 603109833, 5031962899, 939114349, 6022213938, 605667824, 367582180

The Network Insight Report for the specified identifiers presents a detailed analysis of data transmission dynamics. It highlights notable trends, including usage spikes and anomalies that may indicate fluctuating demand on the network. Furthermore, the report addresses potential security vulnerabilities linked to connectivity that require careful scrutiny. Understanding these aspects is crucial for developing effective strategies to enhance network performance and security. What measures can be implemented to address these challenges effectively?
Overview of Analyzed Identifiers
As the analysis of network identifiers commences, it is essential to establish a clear understanding of the various types of identifiers examined.
The identifier analysis focuses on unique numeric sequences, facilitating data comparison across networks. Each identifier serves a distinct purpose, impacting connectivity and data transmission.
This foundational overview sets the stage for a deeper exploration into the significance and implications of these identifiers.
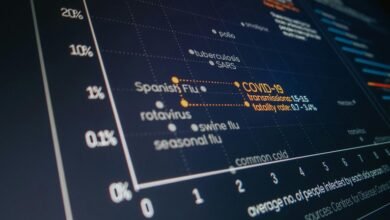
Trends and Patterns Identified
Identifying trends and patterns within network identifiers reveals critical insights into connectivity dynamics and data management strategies.
Analysis indicates notable data anomalies and usage spikes that suggest fluctuating demand and potential system strain.
Understanding these patterns facilitates proactive adjustments, ensuring optimal network performance.
Such insights empower stakeholders to maintain efficiency and reliability, catering to user needs while promoting a liberated data environment.
Vulnerabilities and Security Implications
While network connectivity facilitates seamless communication and data exchange, it simultaneously introduces vulnerabilities that can be exploited by malicious actors.
A rigorous vulnerability assessment is essential to identify these weaknesses. Inadequate security protocols may exacerbate risks, allowing unauthorized access and data breaches.
Organizations must prioritize the evaluation of their security measures to protect sensitive information and maintain the integrity of their network systems.
Recommendations for Network Optimization
To enhance network performance, organizations must adopt a systematic approach to optimization that considers both infrastructure and user requirements.
Effective bandwidth management is essential to allocate resources efficiently, while implementing strategies for latency reduction can significantly improve user experience.
Conclusion
In conclusion, the Network Insight Report underscores the intricate dance between demand and system capacity for the analyzed identifiers. As usage spikes and security vulnerabilities surface, one must ponder: can a network truly thrive without continuous adaptation? The recommendations provided serve as a beacon, guiding the path toward optimized performance and user satisfaction. By embracing these insights, stakeholders can fortify their networks, transforming potential pitfalls into stepping stones for resilience and growth in an ever-evolving digital landscape.